As many as 29,000 network storage devices manufactured by Taiwan-based QNAP are vulnerable to hacks that are easy to carry out and give unauthenticated users on the Internet complete control, a security firm has warned.
The vulnerability, which carries a severity rating of 9.8 out of a possible 10, came to light on Monday, when QNAP issued a patch and urged users to install it. Tracked as CVE-2022-27596, the vulnerability makes it possible for remote hackers to perform a SQL injection, a type of attack that targets web applications that use the Structured Query Language. SQL injection vulnerabilities are exploited by entering specially crafted characters or scripts into the search fields, login fields, or URLs of a buggy website. The injections allow for the modifying, stealing, or deleting of data or the gaining of administrative control over the systems running the vulnerable apps.
QNAP’s advisory on Monday said that network-attached storage devices running QTS versions before 5.0.1.2234 and QuTS Hero versions prior to h5.0.1.2248 were vulnerable. The post also provided instructions for updating to the patched versions.
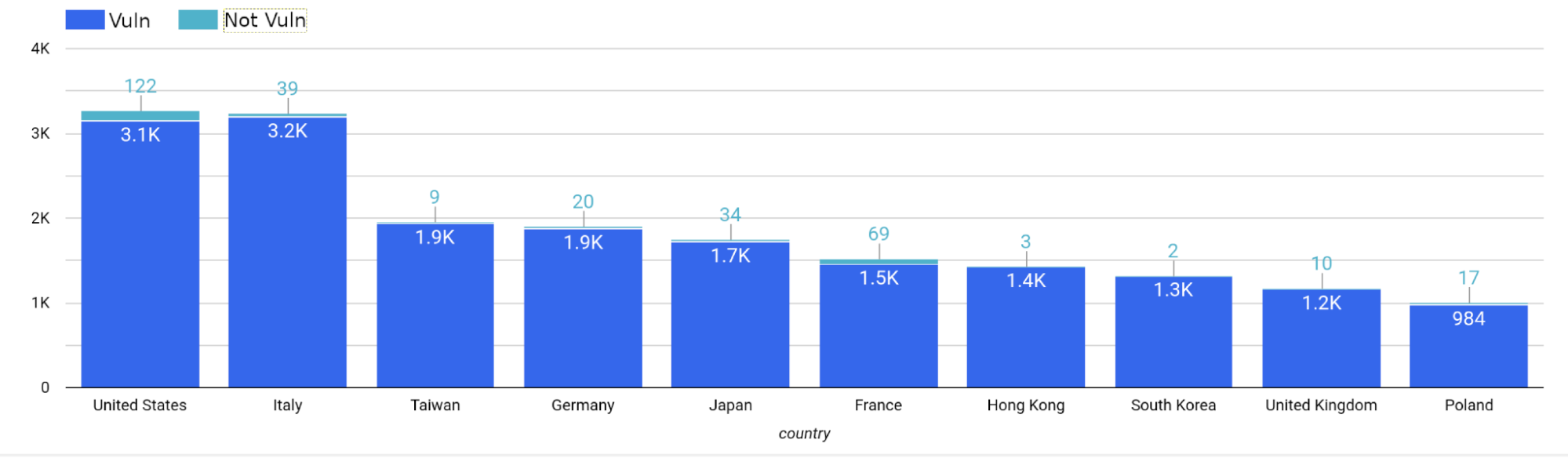
On Tuesday, security firm Censys reported that data collected from network scan searches showed that as many as 29,000 QNAP devices may not have been patched against CVE-2022-27596. Researchers found that of the 30,520 Internet-connected devices showing what version they were running, only 557, or about 2 percent, were patched. In all, Censys said it detected 67,415 QNAP devices. The 29,000 figure was estimated by applying the 2 percent patch rate to the total number of devices.
“Given that the Deadbolt ransomware is geared to target QNAP NAS devices specifically, it’s very likely that if an exploit is made public, the same criminals will use it to spread the same ransomware again,” Censys researchers wrote. “If the exploit is published and weaponized, it could spell trouble to thousands of QNAP users.”


 Loading comments...
Loading comments...
