
A new wave of documents from Edward Snowden's cache of National Security Agency data published by Der Spiegel demonstrates how the agency has used its network exploitation capabilities both to defend military networks from attack and to co-opt other organizations' hacks for intelligence collection and other purposes. In one case, the NSA secretly tapped into South Korean network espionage on North Korean networks to gather intelligence.
The documents were published as part of an analysis by Jacob Appelbaum and others working for Der Spiegel of how the NSA has developed an offensive cyberwarfare capability over the past decade. According to a report by the New York Times, the access the NSA gained into North Korea's networks—which initially leveraged South Korean "implants" on North Korean systems, but eventually consisted of the NSA's own malware—played a role in attributing the attack on Sony Pictures to North Korean state-sponsored actors.
Included with the documents released by Der Spiegel are details on how the NSA built up its Remote Operations Center to carry out "Tailored Access Operations" on a variety of targets, while also building the capability to do permanent damage to adversaries' information systems, including internal NSA newsletter interviews and training materials. Also included was a malware sample for a keylogger, apparently developed by the NSA and possibly other members of the "Five Eyes" intelligence community, which was also included in the dump. The code appears to be from the Five Eyes joint program "Warriorpride," a set of tools shared by the NSA, the United Kingdom's GCHQ, the Australian Signals Directorate, Canada's Communications Security Establishment, and New Zealand's Government Communications Security Bureau.
It's not clear from the report whether the keylogger sample came from the cache of documents provided by former NSA contractor Edward Snowden or from another source. As of now, Appelbaum and Der Spiegel have not yet responded to a request by Ars for clarification. However, Appelbaum has previously published content from the NSA, including the NSA's ANT catalog of espionage tools, that were apparently not from the Snowden cache.
Pwning the pwners
The core of the NSA's ability to detect, deceive, block, and even repurpose others' cyber-attacks, according to the documents, are Turbine and Turmoil, components of the Turbulence family of Internet surveillance and exploitation systems. These systems are also connected to Tutelage, an NSA system used to monitor traffic to and from US military networks, to defend against attacks on Department of Defense systems.
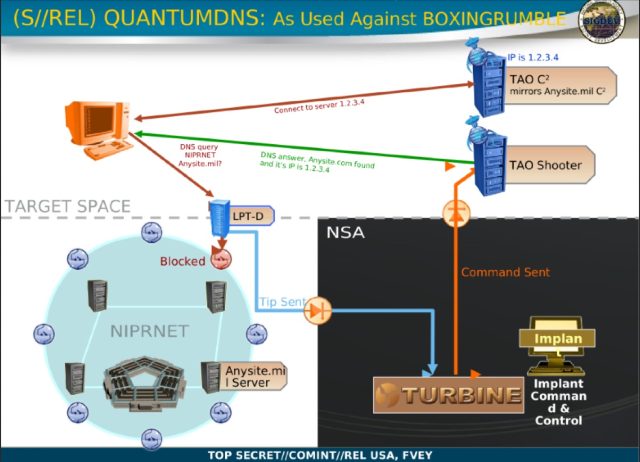
When an attack on a DoD network is detected through passive surveillance (either through live alerts from the Turmoil surveillance filters or processing by the Xkeyscore database), the NSA can identify the components involved in the attack and take action to block it, redirect it to a false target to analyze the malware used in the attack, or do other things to disrupt or deceive the attacker. This all happens outside of DOD's networks, on the public Internet, using "Quantum" attacks injected into network traffic at a routing point.
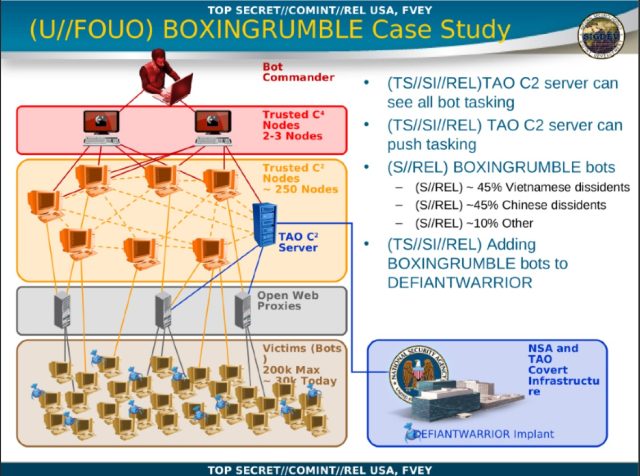
But the NSA can also use others' cyberattacks for its own purposes, including hijacking botnets operated by other actors to spread the NSA's own "implant" malware. Collection of intelligence of a target using another actor's hack of that target is referred to within the signals intelligence community as "fourth party collection." By discovering an active exploit by another intelligence organization or other attacker on a target of interest, the NSA can opportunistically ramp up collection on that party as well, or even use it to distribute its own malware to do surveillance.
In a case study covered in one NSA presentation, the NSA's Tailored Access Office hijacked a botnet known by the codename "Boxingrumble" that had primarily targeted the computers of Chinese and Vietnamese dissidents and was being used to target the DOD's unclassified NIPRNET network. The NSA was able to deflect the attack and fool the botnet into treating one of TAO's servers as a trusted command and control (C&C or C2) server. TAO then used that position of trust, gained by executing a DNS spoofing attack injected into the botnet's traffic, to gather intelligence from the bots and distribute the NSA's own implant malware to the targets.
Spying on spies spying on spies spying...
Things get even more interesting in the case of the NSA's urgent need to gather more intelligence from North Korea's networks. In a question-and-answer posting to the NSA's intranet, an NSA employee recounted a "fifth party" collection that occurred when the NSA hacked into South Korea's exploit of North Korean computers—and ended up collecting data from North Korea's hack of someone else:
While we aren't super interested in [South Korea] (things change a bit when they started targeting us more), we were interested in North Korea and SK put a lot of resources against them. At that point, our access to NK was next to nothing but we were able to make some inroads to the SK CNE [computer network exploitation] program. We found a few instances where there were NK officials with SK implants on their boxes, so we got on the [exfiltration] points, and sucked the data back. That's fourth party. However, some of the individuals that SK was targeting were also part of the NK CNE program. So I guess that would be the fifth party collect...But once that started happening, we ramped up efforts to target NK ourselves (as you don't want to rely on an untrusted actor to do your work for you).
That meant that at one point, the NSA was collecting information via a South Korean implant that had in turn been collected by a North Korean implant. It's not clear whether the NSA's TAO used the existing South Korean malware as an avenue to drop its own, as happened with the "Boxingrumble" botnet.
The poster also noted another occasion when, during an attempt to hack into another target they were trying to exploit, the NSA discovered, "there was another actor that was also going against them and having great success because of a zero day they wrote." The NSA captured the zero day exploit in its passive collection and "were able to repurpose it," the NSA employee recounted. "Big win."
reader comments
85